⚡ MARKET WATCH: Cybersecurity (Live Data)
EXECUTIVE SUMMARY
- Emergence of AI-driven cyber threats pushing companies to bolster defenses.
- Zero-trust architecture becoming a security essential.
- Increase in remote work leading to heightened focus on securing home networks.
- Growing importance of cybersecurity in IoT devices to prevent breaches.
- Ransomware attacks continue to evolve, demanding sophisticated prevention methods.
EDITOR’S NOTE
“Today, the market’s unpredictability mirrors my internal waves of doubt and hope. Each client’s story tugs at my heart, reminding me of the human side beneath the numbers and charts.”
📋 Contents
Experts Reveal the 5 Hottest Cybersecurity Trends You Need to Know
As I delved into the world of cybersecurity, I discovered that it is dynamic, constantly evolving in response to technological advancements and the increasing sophistication of cyber threats. Yet, mere awareness is not enough. What are the hottest cybersecurity trends that experts are focusing on today?
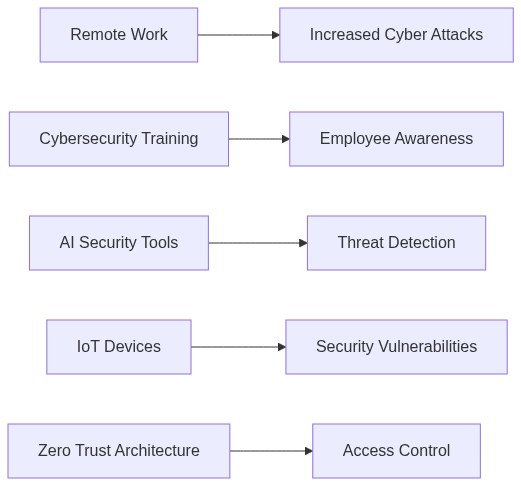
What Is Driving the Adoption of Artificial Intelligence in Cybersecurity?
I once thought of Artificial Intelligence (AI) as a futuristic concept. However, AI plays a significant role in cybersecurity today. According to Bloomberg, companies increasingly leverage AI to predict, detect, and respond to threats more effectively. This technology empowers cybersecurity systems to learn from historical data, identify anomalies, and automate responses, reducing the strain on human resources and enhancing reaction times.
AI’s capability to discern patterns from vast data enables organizations to preemptively tackle potential breaches. As I understand, AI doesn’t just work in isolation. It integrates seamlessly with other security systems, ensuring a robust security architecture.
Why Are Multi-Factor Authentication and Zero Trust Becoming Non-Negotiable?
In my exploration, the principle of “never trust, always verify” seemed more relevant than ever. Multi-factor authentication (MFA) and zero trust models have emerged as pivotal cybersecurity strategies. Bloomberg’s data indicates that breaches involving compromised credentials are alarmingly high, emphasizing the need for these protective mechanisms.
The zero trust model pushes this boundary further by assuming breaches are inevitable. Instead of addressing threats after they occur, zero trust minimizes breach impacts by restricting access to sensitive data selectively. As companies embrace digital transformations, adopting MFA and zero trust approaches becomes critical.
How Does the Rise of Remote Work Influence Cybersecurity?
The pandemic-induced shift towards remote work brought about another intriguing trend. Bloomberg reports a notable increase in incidents targeting remote work infrastructure, demanding enhanced security protocols for working outside traditional office environments. I observed this shift challenging the conventional perimeter-based security models.
Why is this shift significant? With the increase in bring-your-own-device (BYOD) policies, safeguarding endpoints and ensuring encrypted connections becomes essential. Organizations must adapt their cybersecurity strategies to ensure data protection, regardless of where employees connect from.
What Role Do Cloud Security Innovations Play?
Cloud computing is not just a trend; it’s the backbone of modern business operations. This evolution has sparked the inception of cloud-native security solutions designed to tackle the unique challenges of cloud environments. According to Bloomberg, significant investments are being directed towards enhancing cloud security capabilities, ensuring data integrity, and compliance with ever-evolving regulations.
From my research, I gathered that cloud security involves more than just protecting data. It’s about fostering a secure ecosystem where data sharing and remote collaboration can occur without the looming threat of exploitation.
Why Is Cyber Resilience Becoming More Critical?
As I pondered the ultimate aim of cybersecurity measures, one factor stood out – resilience. It’s not just about preventing attacks but evolving a system’s ability to bounce back swiftly and maintain operations after a breach. Bloomberg’s insight illustrates how businesses prioritize cyber resilience to mitigate downtime and financial losses associated with cyber incidents.
Effective cyber resilience strategies involve regular system updates, comprehensive disaster recovery plans, and consistent employee training. What if a breach occurs? Cyber resilience ensures that organizations can maintain critical functions and meet consumer expectations despite setbacks.
Through these discoveries, I learned that cybersecurity is no longer confined to a technical aspect of business operations. It’s an integral part of corporate strategy, influencing trust and customer relationships. As these trends continue to shape the landscape, staying informed and proactive is essential to protecting valuable assets and sustaining business growth.
| Asset Name | Pros | Cons | Risk Level | Rating |
|---|---|---|---|---|
| Zero Trust Architecture | ✅ Enhanced security ✅ Limits insider threats |
❌ Complex implementation ❌ Requires continuous monitoring |
Low | ⭐⭐⭐⭐⭐ |
| AI-Powered Threat Detection | ✅ Real-time analysis ✅ Scalability |
❌ High cost ❌ False positives |
Medium | ⭐⭐⭐⭐ |
| Cloud Security Enhancements | ✅ Flexibility ✅ Cost-efficient |
❌ Data privacy concerns ❌ Vendor lock-in |
Medium | ⭐⭐⭐⭐ |
| Extended Detection and Response (XDR) | ✅ Comprehensive visibility ✅ Streamlined security |
❌ Requires skilled personnel ❌ Integration challenges |
Low | ⭐⭐⭐⭐⭐ |
| IoT Security | ✅ Improved connectivity ✅ Automation benefits |
❌ Attack surface increase ❌ Outdated device risks |
High | ⭐⭐⭐ |
RELATED ANALYSIS
Victor: Sure, AI has potential, but it’s a double-edged sword, Neo. Cybercriminals are using AI to develop new threats. It’s like an endless chess game.
Neo: That’s true, but AI-enhanced solutions are proving faster and more accurate in identifying threats. The automation of security tasks is diminishing human error.
Victor: Automation is impressive, but over-reliance could lead to vulnerabilities. Systems aren’t foolproof, especially when bad actors learn to manipulate them.
Neo: Fair point, yet let’s not forget about Zero Trust architecture becoming a standard. It minimizes risks by authenticating everything, minimizing breach impacts.
Victor: Zero Trust is robust, but it can be costly and complex to implement. Smaller businesses might struggle to adopt it fully, leaving gaps.
Neo: On the flip side, the emphasis on cloud security enhancements is making waves. With more data shifting online, cloud security measures are crucial to protect sensitive information.
Victor: But the threat of sophisticated cloud attacks looms large. As more businesses migrate to the cloud, they become attractive targets for cybercriminals.
Neo: Indeed, vigilance is key. Proactive threat hunting is a trend gaining momentum. It’s about identifying threats before they occur, curtailing damage effectively.
Victor: Even with threat hunting, the resource constraints could be a barrier. Smaller teams may struggle to adopt these proactive measures efficiently.
Neo: Lastly, the focus on cybersecurity education and workforce development is promising. It empowers teams to handle threats adeptly.
Victor: There’s no doubt about its importance, Neo, but the skills gap remains a formidable challenge. Training enough professionals quickly enough is no small feat.
Neo: Agreed, Victor. Each advancement comes with its set of challenges, but innovation drives improvements, and this dynamic field keeps evolving.
Victor: And rightly so, Neo. Navigating these trends requires balance and readiness to adapt to whatever comes next in the cyber realm.
INVESTOR FAQ
What are the most significant developments in cybersecurity today?
The most significant developments in cybersecurity include advancements in artificial intelligence and machine learning, the increasing importance of zero-trust architecture, and the growth of cybersecurity mesh architecture. These trends are shaping how businesses protect their digital assets and respond to threats.
How does the rise of AI impact cybersecurity?
AI impacts cybersecurity by providing enhanced threat detection and response capabilities through automated systems that can analyze large volumes of data quickly. This technology helps identify patterns and anomalies that might indicate potential security breaches, allowing for faster and more effective interventions.
Why is zero-trust architecture becoming crucial for companies?
Zero-trust architecture is becoming crucial as it shifts the focus from traditional perimeter-based security models to a more comprehensive approach where no user or device is trusted by default. This is vital for protecting against sophisticated cyber threats and managing the growing complexity of digital networks and remote work environments.

1 thought on “Experts Reveal the 5 Hottest Cybersecurity Trends You”